Jump To: Support > KB > NetManager > SSLIntercept
Pitfalls with HTTPS interception
Certificates
You need to install a certificate from the proxy on all devices otherwise you will get certificate errors. With Active Directory, this is easy enough, but on other devices it may be much more problematic.
Scope of what is being intercepted
Once you have a certificate present, the proxy may intercept all https sites without your knowledge.
It's an arms race
Browser makers want you to trust their security, they want to close off all avenues for man-in-the-middle attacks such as HTTPS interception. Things like Certificate pinning may may it ineffective. So software needs to be kept up to date and behaviour may change unexpectedly (making debugging difficult).
Reduced security
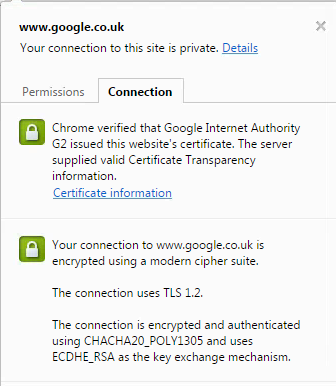
Here's real Google security:
Here's the pretend spoofed up Google security showing old ciphers, browser errors, outdated signatures and old TLS versions:
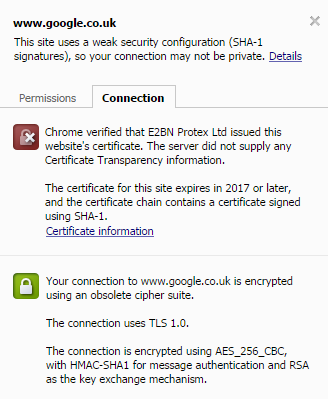
All that and you don't know what secure sites are being intercepted as they can do it without your knowledge (how about your online banking?)
Which would you trust?