Jump To: Support > KB > NetManager > Ssh
Secure Shell (ssh)
Secure Shell is a secure method of getting a CLI on NetManager. It can also be used to secure other tools such as web-access, webadmin and Remote Desktop.
A common ssh program for Windows is PuTTY. For more information see:
Security recommendations
By default, ssh access is blocked by the NetManager firewall and ssh access is allowed to all regular users (but no NetManager inbuilt system users except for ncadmin). This means that users on your LAN (or other trusted networks such as VPN connections) can use ssh, scp or sftp. Users do not not have interactive accounts by default and so will not be able to get to a command line (instead they will be taken to a console-based email client). Please note that the root account is not allowed to log in over ssh with a password; to login as root, you need to follow the instructions here or use ssh keys. To use ssh keys to connect to other NetManagers or Linux/BSD servers with ssh, create keys as described here.
Before opening up firewall access to ssh to allow remote access, we recommend you lock down access further unless you are confident about the complexity of passwords for all users.
The Security > ssh tab in webadmin allows you to customise the settings:
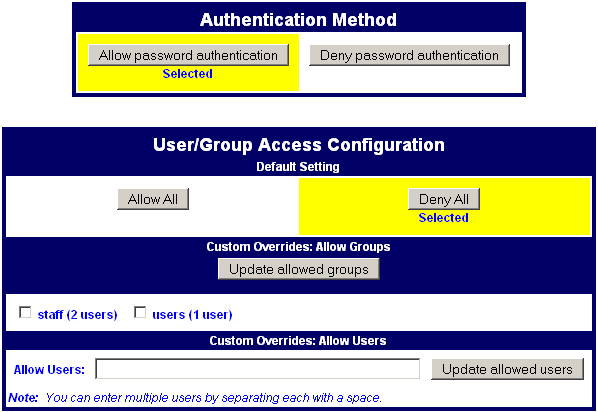
Our recommendations are to do at least one of:
- Deny password authentication - you will need to set up ssh keys to access
- Deny all users - you can then allow just the users you want to have ssh access
Once you have done this, you can open up ssh in the firewall from either the Console Menu or webadmin.
Configuration file directives
Deny password authentication corresponds to sshd_nopass="y"
sshd_group_deny and sshd_user_deny to space-separated lists of groups and users):sshd_user_allow="" sshd_group_allow="" sshd_group_deny="staff" sshd_user_deny="baduser"Deny all users with no overrides corresponds to:
sshd_user_allow="" sshd_group_allow="" sshd_user_deny="*" sshd_group_deny=""Deny all users with certain users/groups allowed corresponds to (set
sshd_group_allow and sshd_user_allow to space-separated lists of groups and users):sshd_group_deny="" sshd_group_allow="staff" sshd_user_deny="" sshd_user_allow="gooduser"
After editing the configuration file, run the ssh build script.