NetManager: Web-filtering
Protecting your users is increasing important
In the modern age of Bring Your Own Device, phishing attacks and terrorist threats, it is crucial that Internet access is controlled and monitored.
Web proxy
A web proxy sits between your client computers and the Internet, fetching web pages on their behalf. A cache is usually incorporated which means that pages that have been viewed once are stored on the server. This means that viewing the page a second time (on any client computer) is much quicker. This is particularly useful in schools where multiple pupils may be viewing the same web pages. Even a fast broadband connection is an order of magnitude slower than your local network.
Fine filtering
Having a local proxy also allows you to filter access to websites. Even if your ISP provides filtered web access, it is often very useful to block extra websites (such as Hotmail). You may use automatically updated lists of blocked sites which are sorted by category (e.g. sex, violence, illegal software). In addition to the automated lists, the NetManager offers you fine-grained control over web access. For example, you could configure the library computers so that they can only access the BBC website between 12 and 2pm. You may set filters for different users, groups, computers, time of day, filenames and, of course, websites. These can be combined in numerous ways to form whitelists and blacklists. All configuration is web-based.
Blacklists and phraselists
NetManager will download daily updates of blacklisted sites containing many millions of inappropriate or malicious sites. Example categories include:
- Violence
- Pornography
- Social Media
- Drugs
- Proxy-bypass sites
In addition to the millions of blacklisted sites, the content of web-pages can be analysed for specific content. This isn't just a simple yes/no. Phrases within the pages can be detected and assigned a score (positive or negative). This means that suitable content (e.g. medical sites) should not be confused with inappropriate sites (e.g. adult-content).
Enforce safe search
NetManager can enforce safe search on Google, Bing and YouTube for certain users or computers.Transparent filtering
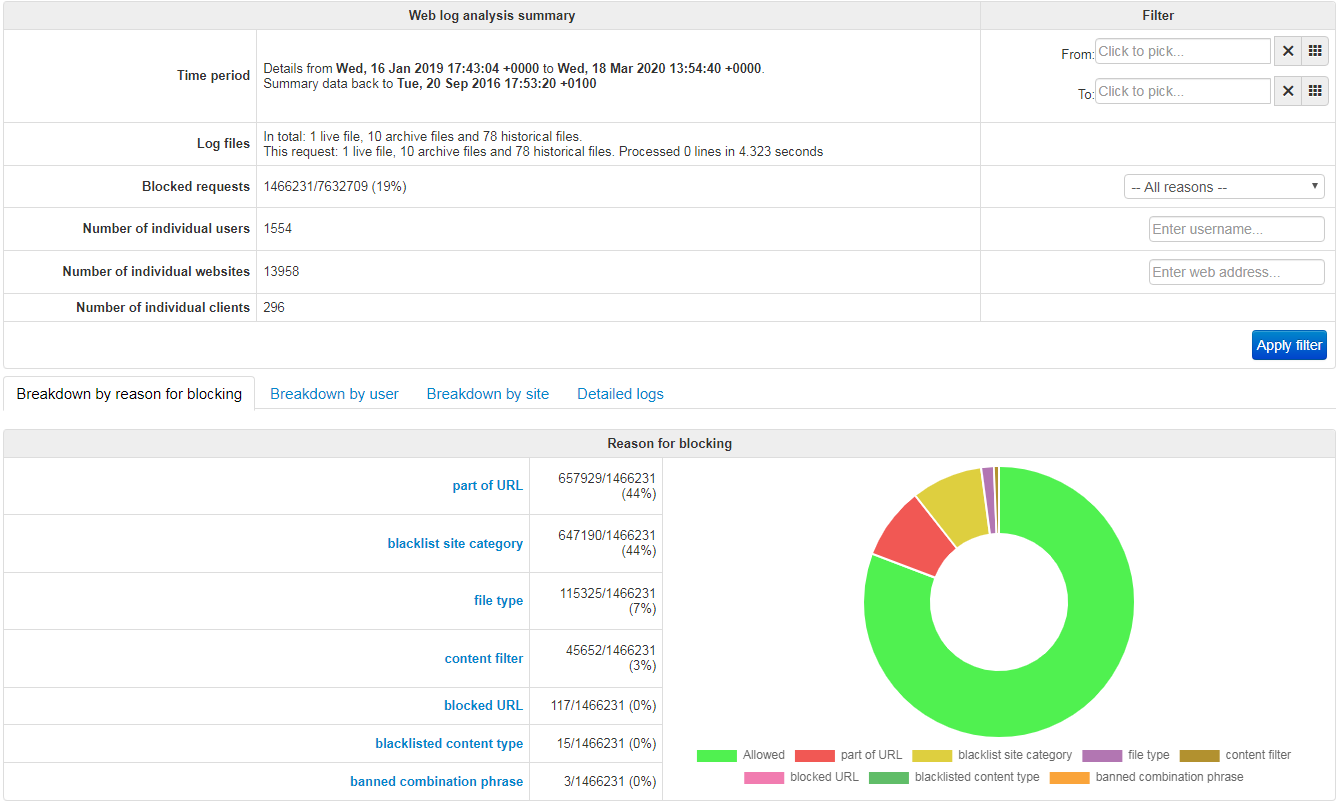
NetManager can intercept web traffic and force it via the web-filtering even if your devices are not set to use a proxy. This is particularly relevant for BYOD. For instance, it is possible to seamlessly block social media and ensure that all other access is logged for pupils' devices. There is also the option to decrypt secure web access (HTTPS interception and decryption) allowing you to log all search engine queries or block only part of a secure website.Analysis and reporting
All web accesses via the proxy are logged and the logs are available through a web-based interface. The logs are fully searchable by time, computer, text and username.
Pro-active reports can be emailed to the administrator when a user/device attempts to access chosen categories of blacklisted sites.
Firewalling
NetManager can act as both an internal and external firewall. it is fully VLAN-aware so can integrate with the most complex network structures and separate wifi networks.- Secure access to internal resources you want to access from the outside (e.g. Moodle, Outlook Web Access)
- Block access to certain Internet resources from specific networks and machines (e.g. stopping direct web access except on a guest network)
- Control access between VLANs within the site (e.g. allow segregation of core IT systems from the rest of the network