WindowsPhotoViewer10
Jump To: Support > KB > Windows > WindowsPhotoViewer10
Getting Windows Photo Viewer back on Windows 10 (and Server 2019)
Our most frequent complaint after migrating users to Windows 10 is that photos no longer open in Windows Photo Viewer. Thanks to some excellent work by Winhelponline.com, it is easy to restore Windows Photo Viewer on Windows 10.
For full details see their site, but we are also hosting the registry file required here for backup purposes.
Notes on our usage of Windows Photo Viewer
w10-wpv-restore.regis copied into NETLOGON- The registry file is imported into the registy as a GPO-based computer startup script using
C:\Windows\system32\reg.exe import \\domain.internal\netlogon\w10-wpv-restore.reg: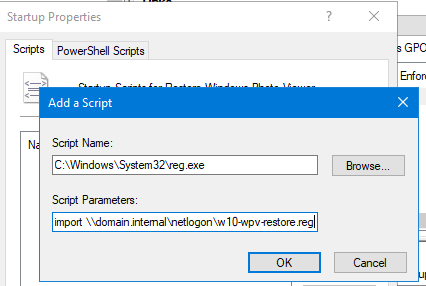
- The GPO has a WMI filter set for is Windows 10 or Server 2016+
- It is used in conjunction with SetUserFTA to set Windows Photo Viewer as the default handler for JPEGs, etc.